best-practices enterprices network and security access distribution core cisco design
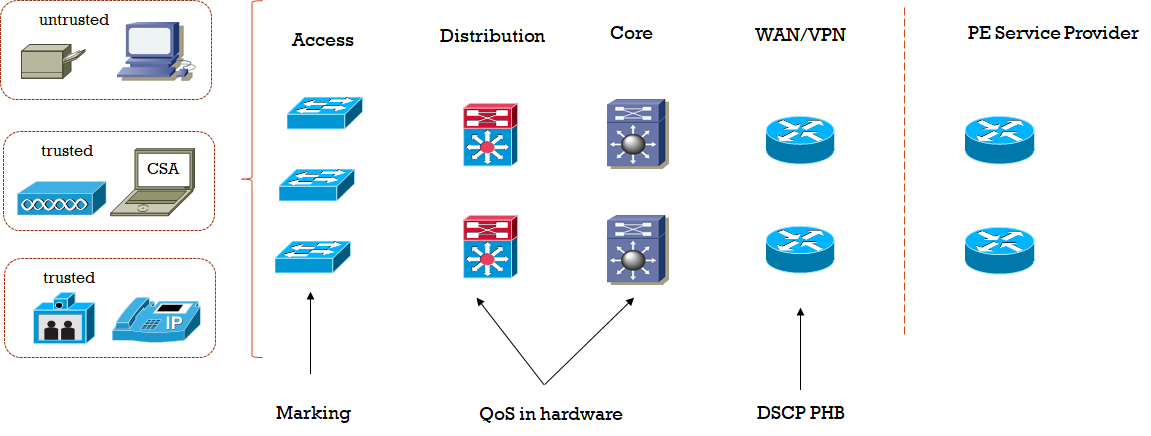
22.12 2019 | by massimilianoEnterprices network and security access distribution core best-practices cisco design 1) Enterprices Building Access Module and Best-Practices: […]
https://www.ingegnerianetworking.com/wp-content/uploads/2019/12/access-module-35a.png
Enterprices network and security access distribution core best-practices cisco design
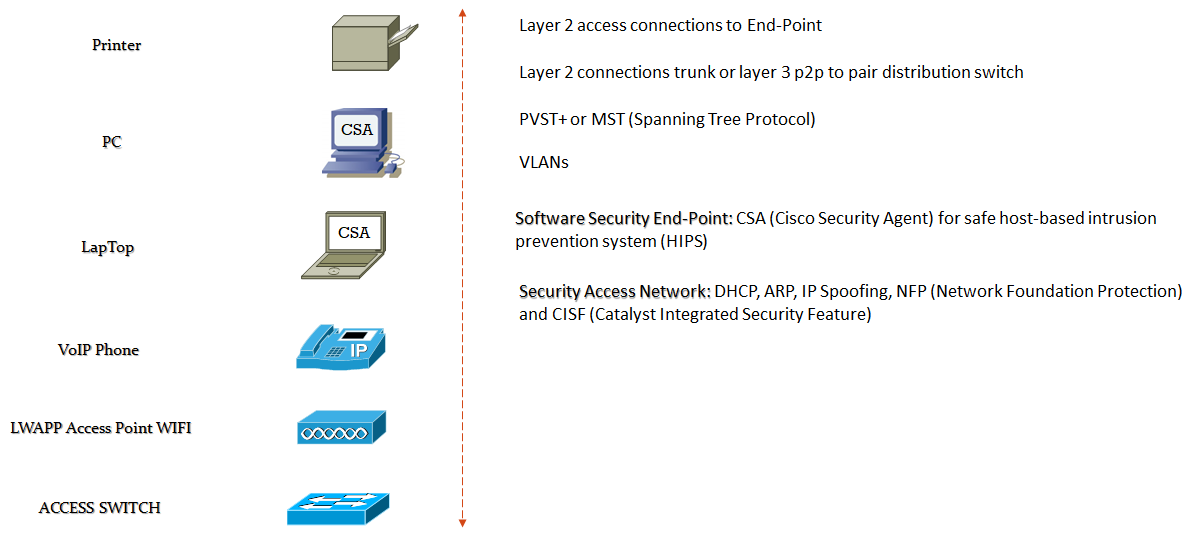
1) Enterprices Building Access Module and Best-Practices:
- Security Infrastructure Level
- – Implement OOB (Out Of Band) interface to devices network management
- – Limit the accessible port devices and restrict the permitted communications
- – Legal Notification
- – Authenticate and Authorize access using AAA
- – Log and Account for all access
- – Protect sensitive data such as local-password
- Security Routing Level (for layer 3 access routing)
- – Authentication router neighbors
- – Use default passive interface
- – Log neighbor changes
- – Implement stub-routing when possible
- Security Device Level
- – Disable unnecessary services
- – Filter and rate-limit control-plane traffic
- – Redundancy
- Security Network Telemetry
- – NTP (Network Time Protocol) to synchronize time to all network domain
- – Monitor interface statistics to all devices
- – Monitor system status information such as CPU, memory and process
- – Log all system status, traffic analysis, access device informations
- Security Policy Enforcement:
- – Implement management and infrastructure ACL (i-ACL)
- – Protect against IP spoofing with uRPF on routed edge interface and with IP source guard on access port
- Security Switching Level
- – Restrict broadcast domain
- – Implement Spanning Tree Protocol against loops (RSTP, RPVST+) and BPDU guard, STP root guard
- – DHCP snooping enable on access vlans against dhcp starvation and rogue dhcp servers attacks
- – IP spoofing protecton with IP source guard enable on access port
- – ARP spoofing protection with dynamic ARP inspection (DAI) enable on access vlans
- – MAC flooding protection with port security enable on access port
- – Broadcast and Multicast protection with storm control enable on access port
- Security i-ACL level
- – A carefully planned addressing scheme
- – Ping and traceroute allowed
- – Block access to address assigned to the infrastructure devices
- – Block access to address assigned to the network management devices
- – Permit client transit traffic
- Security Vlans Level
- – Restrict vlans on single switch
- – Configure separate vlans to voice and data
- – Disable vlans dynamic trunk negotiation trunking on access port (DTP off)
- – Configure explicity trunk mode on infrastructure ports rather autonegotiation
- – Use VTP mode transparent on switches
- – Disable unused ports (shutdown)
- – Do not use vlan 1 for anything
- – Use all tagged mode for native vlan on trunks port
- IBNS ( Identity-Based Networking Services)
- https://www.massimilianosbaraglia.it/switching/34-ibns/62-802-1x-example-guide-config
- – 802.1x
- – MAB (MAC Authentication Bypass)
- NAC Appliance
- https://www.massimilianosbaraglia.it/switching/34-ibns/105-nac-network-admission-control-funzionalita-ed-esempio-di-progetto
- – Implemented on in-band or out-of-band
- – NAC servers and NAC manager placement
- – Access switch vlans requirements
- – Client redirection to NAC server
- – NAC agent
- – Client authentication
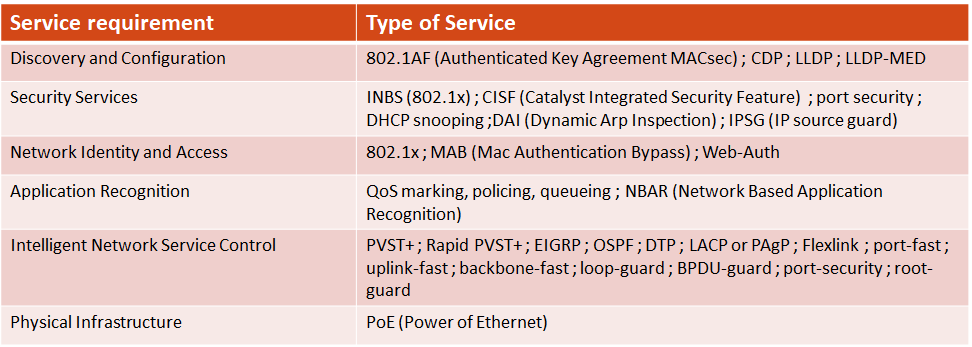
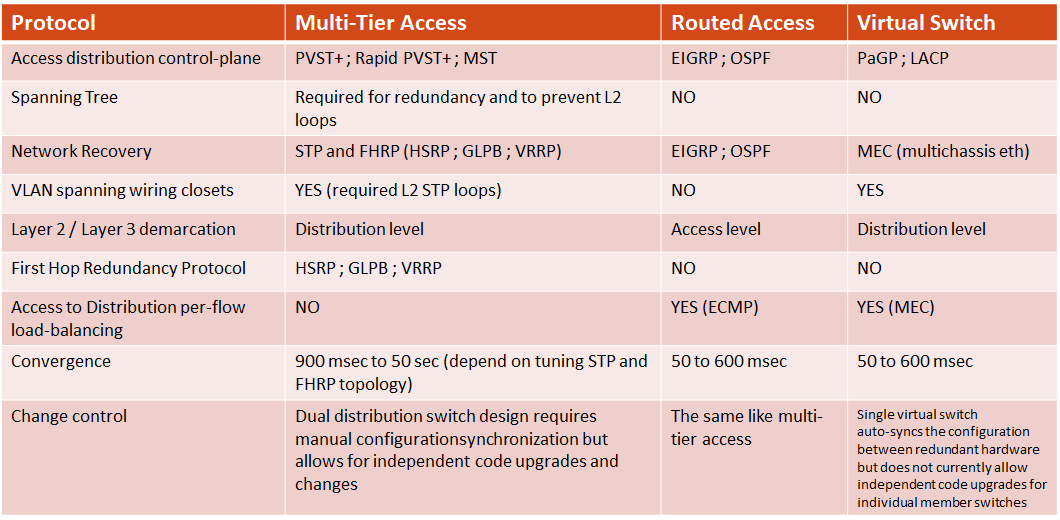
Enterprices security access type of services:
Enterprices Building Access Module traffic recovery:

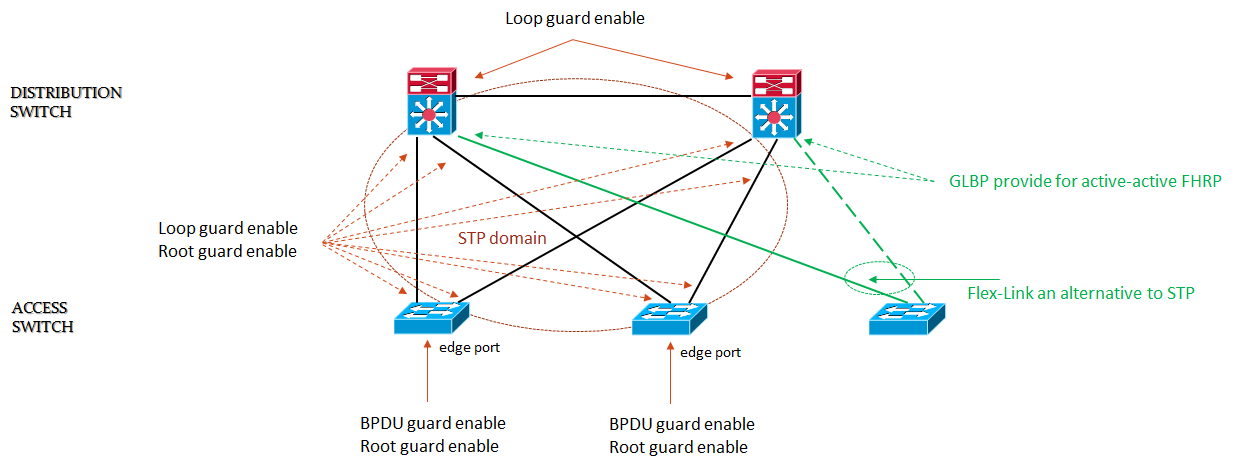
Enterprices Building Access Module STP Topology:
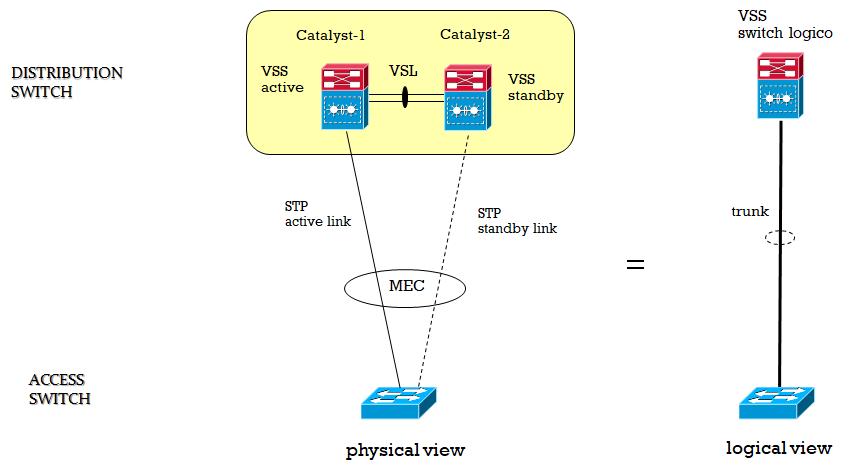
Enterprices Building Access Module Virtual-Switch Star Topology:
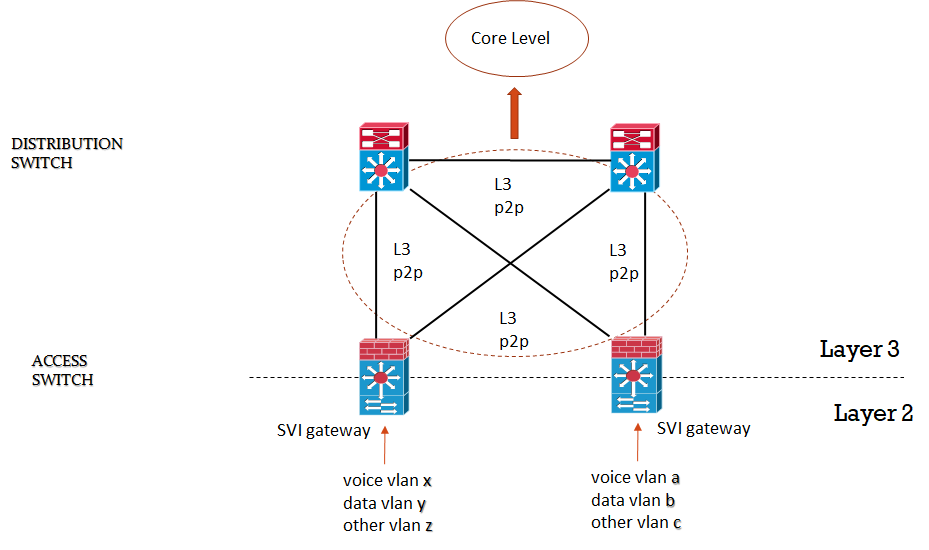
Enterprices Building Access Module Routed Topology:
2) Enterprices Building Distribution Module and Best-Practices:
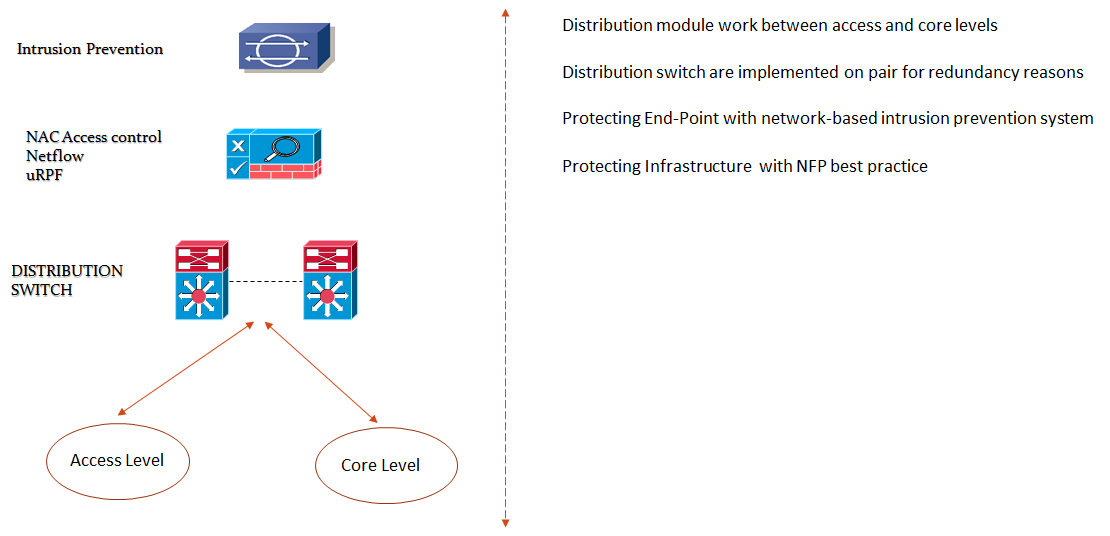
- Security IPS Level
- – Provide filtering of know network worm and virus, DoS traffic attacks, hacking attacks
- – IPS is placed in traffic path (inline mode with bridged traffic) or in promiscuous mode via SPAN, RSPAN, VACL
- – Multiple IPS sensor may offer scalability and availability with load-balancing using ether-channel (ECLB)
- – IPS sensor may be used to see traffic on both directions (traffic symmetry)
- Security Infrastructure Level
- – Implement OOB (Out Of Band) interface to devices network management
- – Limit the accessible port devices and restrict the permitted communications
- – Legal Notification
- – Authenticate and Authorize access using AAA
- – Log and Account for all access
- – Protect sensitive data such as local-password
- Security Routing Level
- – Authentication router neighbor
- – Use default passive interface
- – Log neighbor changes
- – Implement stub-routing when possible
Note: Route filtering and stub routing in the distribution layer are only recommended for a multi-tier or VSS design where the routed edge interface is on the distribution switches. In a routed access design, these features are used in the access layer.
- Security Device Level
- – Disable unnecessary services
- – Filter and rate-limit control-plane traffic
- – Redundancy
- Security Network Telemetry
- – NTP (Network Time Protocol) to synchronize time to all network domain
- – Monitor interface statistics to all devices
- – Monitor system status information such as CPU, memory and process)
- – Log all system status, traffic analysis, access device information
- – Enable Netflow
- Security Policy Enforcement:
- – Implement management and infrastructure ACL (i-ACL)
- – Protect against IP spoofing with uRPF on routed edge interface
Note: uRPF is only applicable in the distribution layer of a multi-tier design where the routed edge interface is on the distribution switches. In a routed access design, this is enabled in the access layer.
- Security Switching Level
- – Restrict broadcast domain
- – Implement Spanning Tree Protocol against loops (RSTP, RPVST+) and BPDU guard, STP root guard
- – Implement vlans best practice
Note: VLAN and spanning tree best practices are only applicable in the distribution layer of a multi-tier design where Layer 2 extends to the distribution layer switches.
Enterprices Security Distribution Models:
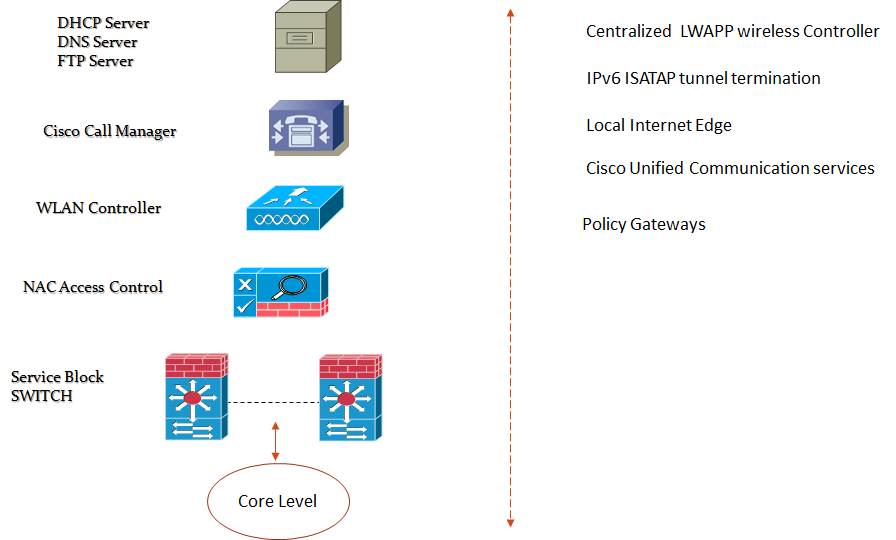
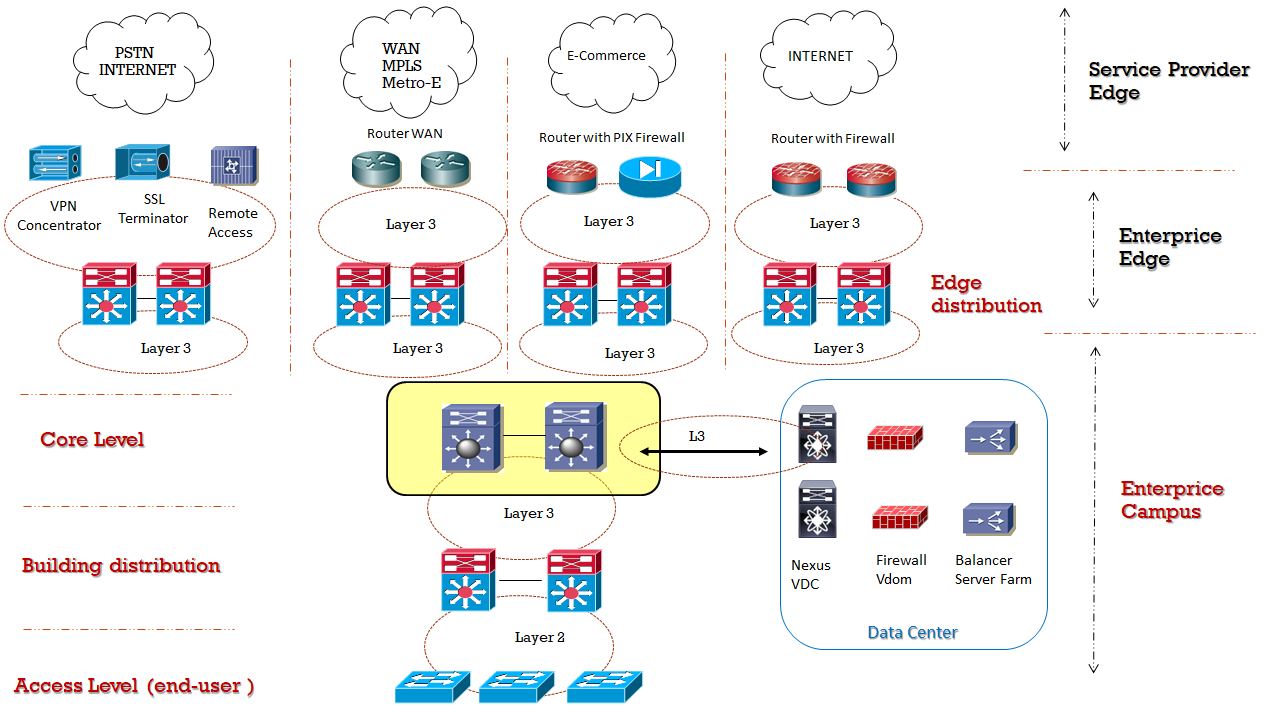
3) Enterprices Building Services Block and Best-Practices:
4) Enterprices Building Core and Best-Practices:
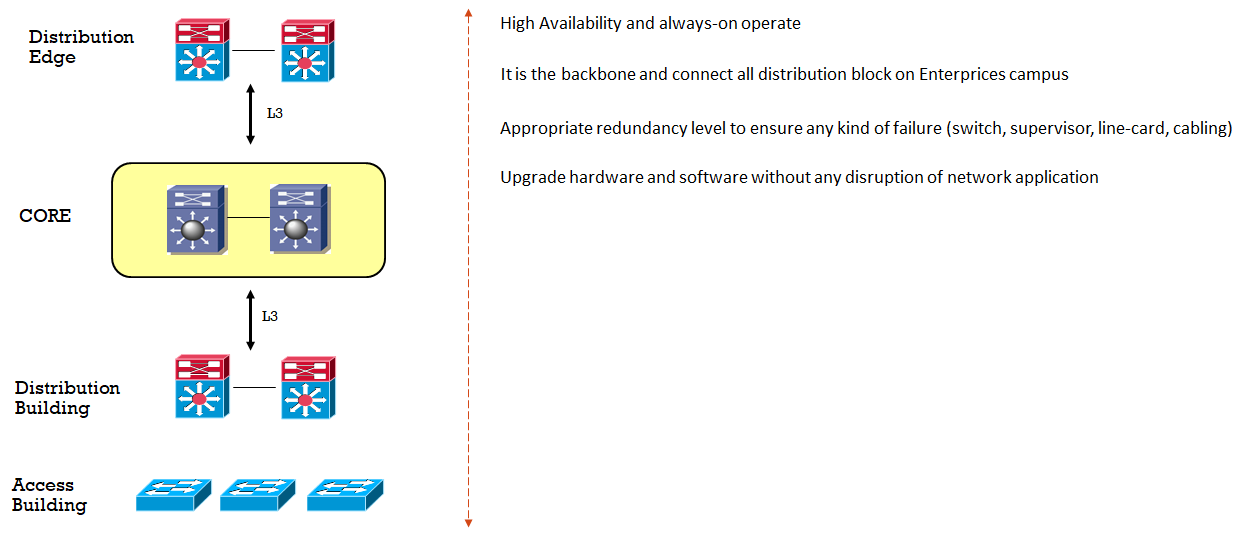
Enterprices Architecture Core Models:
5) Enterprices Building QoS and Best-Practices: