test-lab mpls inter-as option B con cisco config (senza RRs) e l’importanza del comando “mpls bgp forwarding”
04.04 2020 | by massimilianoTest-Lab mpls Inter-AS option B con cisco config (senza RRs) e l’importanza del comando ” mpls bgp forwarding “ ARCHITETTURA […]
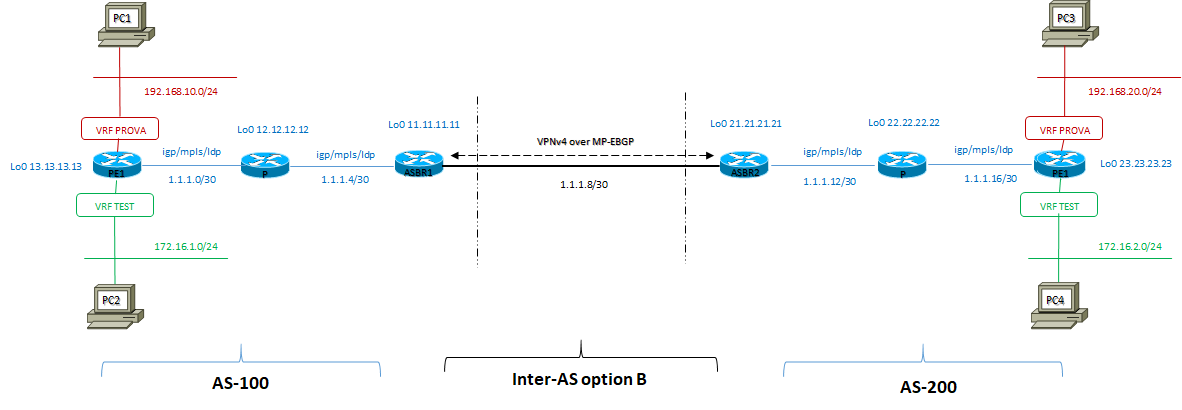
https://www.ingegnerianetworking.com/wp-content/uploads/2020/04/lab-test-mpls-option-b-4ce.png
Test-Lab mpls Inter-AS option B con cisco config (senza RRs) e l’importanza del comando ” mpls bgp forwarding “
ARCHITETTURA DI RIFERIMENTO
CONFIG DOMAIN AS-100
| PE1 | P router | ASBR1 |
|
ip vrf PROVA ! mpls label protocol ldp ! interface Loopback0 interface GigabitEthernet0/3 router ospf 100 ! router bgp 100 |
mpls label protocol ldp ! interface Loopback0 router ospf 100 |
mpls label protocol ldp ! interface Loopback0 ! interface GigabitEthernet0/1 mpls bgp forwarding router ospf 100 ! router bgp 100 |
CONFIG DOMAIN AS-200
| PE2 | P router | ASBR2 |
|
ip vrf PROVA mpls label protocol ldp ! interface Loopback0 interface GigabitEthernet0/3 router bgp 200 |
mpls label protocol ldp ! interface Loopback0 router ospf 200
|
mpls label protocol ldp ! interface Loopback0 interface GigabitEthernet0/1 mpls bgp forwarding ! router ospf 200 router bgp 200 |
Di seguito vediamo gli output di interesse per il solo protocollo BGP:
I router ASBR hanno il ruolo di PE edge lato AS100 domain ed inoltre sono ASBR stabilendo una sessione EBGP VPNv4 tra differenti AS
I router ASBR non mantengono le prefix L3VPN; le relative routes sono solo mantenute a livello di BGP VPNv4 table:
ASBR1#show ip route 192.168.10.0
% Network not in table
ASBR1#show ip route vrf TEST
% IP routing table vrf TEST does not exist
ASBR1#show ip route vrf PROVA
% IP routing table vrf PROVA does not exist
ASBR1#show ip bgp vpnv4 all
BGP table version is 5, local router ID is 11.11.11.11
Status codes: s suppressed, d damped, h history, * valid, > best, i – internal,
r RIB-failure, S Stale, m multipath, b backup-path, f RT-Filter,
x best-external, a additional-path, c RIB-compressed,
Origin codes: i – IGP, e – EGP, ? – incomplete
RPKI validation codes: V valid, I invalid, N Not found
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 100:10
*>i 172.16.1.0/24 13.13.13.13 0 100 0 ?
*> 172.16.2.0/24 1.1.1.1 0 0 200 ?
Route Distinguisher: 200:200
*>i 192.168.10.0 13.13.13.13 0 100 0 ?
*> 192.168.20.0 1.1.1.1 0 0 200 ?
ASBR2#show ip bgp vpnv4 all
BGP table version is 7, local router ID is 21.21.21.21
Status codes: s suppressed, d damped, h history, * valid, > best, i – internal,
r RIB-failure, S Stale, m multipath, b backup-path, f RT-Filter,
x best-external, a additional-path, c RIB-compressed,
Origin codes: i – IGP, e – EGP, ? – incomplete
RPKI validation codes: V valid, I invalid, N Not found
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 100:10
*> 172.16.1.0/24 1.1.1.9 0 100 ?
*>i 172.16.2.0/24 23.23.23.23 0 100 0 ?
Route Distinguisher: 200:200
*> 192.168.10.0 1.1.1.9 0 100 ?
*>i 192.168.20.0 23.23.23.23 0 100 0 ?
I router PE hanno tutte le prefix L3VPN appartenenti alle VRF di pertinenza nelle loro rispettive tabelle di routing:
PE1#show ip route vrf PROVA
Routing Table: PROVA
Codes: L – local, C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route, H – NHRP, l – LISP
a – application route
+ – replicated route, % – next hop override, p – overrides from PfR
Gateway of last resort is not set
192.168.10.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.10.0/24 is directly connected, GigabitEthernet0/1
L 192.168.10.1/32 is directly connected, GigabitEthernet0/1
B 192.168.20.0/24 [200/0] via 11.11.11.11, 04:30:38
PE1#show ip route vrf TEST
Routing Table: TEST
Codes: L – local, C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route, H – NHRP, l – LISP
a – application route
+ – replicated route, % – next hop override, p – overrides from PfR
Gateway of last resort is not set
172.16.0.0/16 is variably subnetted, 3 subnets, 2 masks
C 172.16.1.0/24 is directly connected, GigabitEthernet0/3
L 172.16.1.1/32 is directly connected, GigabitEthernet0/3
B 172.16.2.0/24 [200/0] via 11.11.11.11, 04:33:51
PE1#show ip bgp vpnv4 all
BGP table version is 8, local router ID is 13.13.13.13
Status codes: s suppressed, d damped, h history, * valid, > best, i – internal,
r RIB-failure, S Stale, m multipath, b backup-path, f RT-Filter,
x best-external, a additional-path, c RIB-compressed,
Origin codes: i – IGP, e – EGP, ? – incomplete
RPKI validation codes: V valid, I invalid, N Not found
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 100:10 (default for vrf TEST)
*> 172.16.1.0/24 0.0.0.0 0 32768 ?
*>i 172.16.2.0/24 11.11.11.11 0 100 0 200 ?
Route Distinguisher: 200:200 (default for vrf PROVA)
*> 192.168.10.0 0.0.0.0 0 32768 ?
*>i 192.168.20.0 11.11.11.11 0 100 0 200 ?
PE2#show ip route vrf PROVA
Routing Table: PROVA
Codes: L – local, C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route, H – NHRP, l – LISP
a – application route
+ – replicated route, % – next hop override, p – overrides from PfR
Gateway of last resort is not set
B 192.168.10.0/24 [200/0] via 21.21.21.21, 04:36:03
192.168.20.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.20.0/24 is directly connected, GigabitEthernet0/1
L 192.168.20.1/32 is directly connected, GigabitEthernet0/1
PE2#show ip route vrf TEST
Routing Table: TEST
Codes: L – local, C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route, H – NHRP, l – LISP
a – application route
+ – replicated route, % – next hop override, p – overrides from PfR
Gateway of last resort is not set
172.16.0.0/16 is variably subnetted, 3 subnets, 2 masks
B 172.16.1.0/24 [200/0] via 21.21.21.21, 04:36:46
C 172.16.2.0/24 is directly connected, GigabitEthernet0/3
L 172.16.2.1/32 is directly connected, GigabitEthernet0/3
MA SENZA IL COMANDO ” MPLS BGP FORWARDING” sotto le rispettive interface di peering EBGP VPNv4 i PC locali ad un AS non raggiungono i rispettivi PC dell’altro AS appartenenti alla medesima VRF
Esempio:
PC2> ping 172.16.2.20
172.16.2.20 icmp_seq=1 timeout
172.16.2.20 icmp_seq=2 timeout
172.16.2.20 icmp_seq=3 timeout
172.16.2.20 icmp_seq=4 timeout
172.16.2.20 icmp_seq=5 timeout
PC4> ping 172.16.1.10
172.16.1.10 icmp_seq=1 timeout
172.16.1.10 icmp_seq=2 timeout
172.16.1.10 icmp_seq=3 timeout
172.16.1.10 icmp_seq=4 timeout
172.16.1.10 icmp_seq=5 timeout
CON IL COMANDO ” MPLS BGP FORWARDING ” abilitato:
Esempio:
ASBR1#show run int gi0/2
Building configuration…
Current configuration : 157 bytes
!
interface GigabitEthernet0/2
description to-ASBR2
ip address 1.1.1.9 255.255.255.252
mpls bgp forwarding
end
ASBR2#show run int gi0/2
Building configuration…
Current configuration : 158 bytes
!
interface GigabitEthernet0/2
description to-ASBR1
ip address 1.1.1.10 255.255.255.252
mpls bgp forwarding
end
Abbiamo:
PC2> ping 172.16.2.20
172.16.2.20 icmp_seq=1 timeout
172.16.2.20 icmp_seq=2 timeout
84 bytes from 172.16.2.20 icmp_seq=3 ttl=58 time=8.474 ms
84 bytes from 172.16.2.20 icmp_seq=4 ttl=58 time=8.601 ms
84 bytes from 172.16.2.20 icmp_seq=5 ttl=58 time=8.187 ms
PC2> ping 172.16.2.20
84 bytes from 172.16.2.20 icmp_seq=1 ttl=58 time=10.262 ms
84 bytes from 172.16.2.20 icmp_seq=2 ttl=58 time=10.279 ms
84 bytes from 172.16.2.20 icmp_seq=3 ttl=58 time=8.512 ms
84 bytes from 172.16.2.20 icmp_seq=4 ttl=58 time=8.428 ms
84 bytes from 172.16.2.20 icmp_seq=5 ttl=58 time=8.116 ms
PC2>
PC4>
PC4> ping 172.16.1.10
84 bytes from 172.16.1.10 icmp_seq=1 ttl=58 time=9.781 ms
84 bytes from 172.16.1.10 icmp_seq=2 ttl=58 time=11.000 ms
84 bytes from 172.16.1.10 icmp_seq=3 ttl=58 time=7.548 ms
84 bytes from 172.16.1.10 icmp_seq=4 ttl=58 time=8.014 ms
84 bytes from 172.16.1.10 icmp_seq=5 ttl=58 time=9.279 ms
Il motivo di questo comando è perchè abbiamo la necessità di abilitare i nostri ASBR a trasmettere e ricevere pacchetti labeled attraverso il peering costituito da una sessione EBGP VPNv4.
ASBR1#show mpls forwarding-table
Local Outgoing Prefix Bytes Label Outgoing Next Hop
Label Label or Tunnel Id Switched interface
16 16 13.13.13.13/32 0 Gi0/1 1.1.1.5
17 Pop Label 12.12.12.12/32 0 Gi0/1 1.1.1.5
18 17 192.168.50.0/24 0 Gi0/1 1.1.1.5
19 Pop Label 1.1.1.0/30 0 Gi0/1 1.1.1.5
20 21 200:200:192.168.10.0/24 \
530 Gi0/1 1.1.1.5
21 20 100:10:172.16.1.0/24 \
2650 Gi0/1 1.1.1.5
22 Pop Label 1.1.1.10/32 0 Gi0/2 1.1.1.10
23 22 200:200:192.168.20.0/24 \
510 Gi0/2 1.1.1.10
24 23 100:10:172.16.2.0/24 \
2550 Gi0/2 1.1.1.10